From Repo to Resume: Deploying My Resume App in the Gallifrey Cluster
Building a resume is one thing.
Running it as a production-grade application in your own Kubernetes cluster is something else entirely.
This post documents how I deployed my resume application into my Gallifrey cluster, a Talos-based, bare-metal Kubernetes environment in my homelab, and the patterns I used to treat it like any other real-world workload.
This was not about making a website available.
It was about validating architecture, automation, and operational discipline.
Deployment Flow Overview
Before diving into the individual components, it helps to see the full lifecycle of the application, from a Git commit to a publicly accessible service.
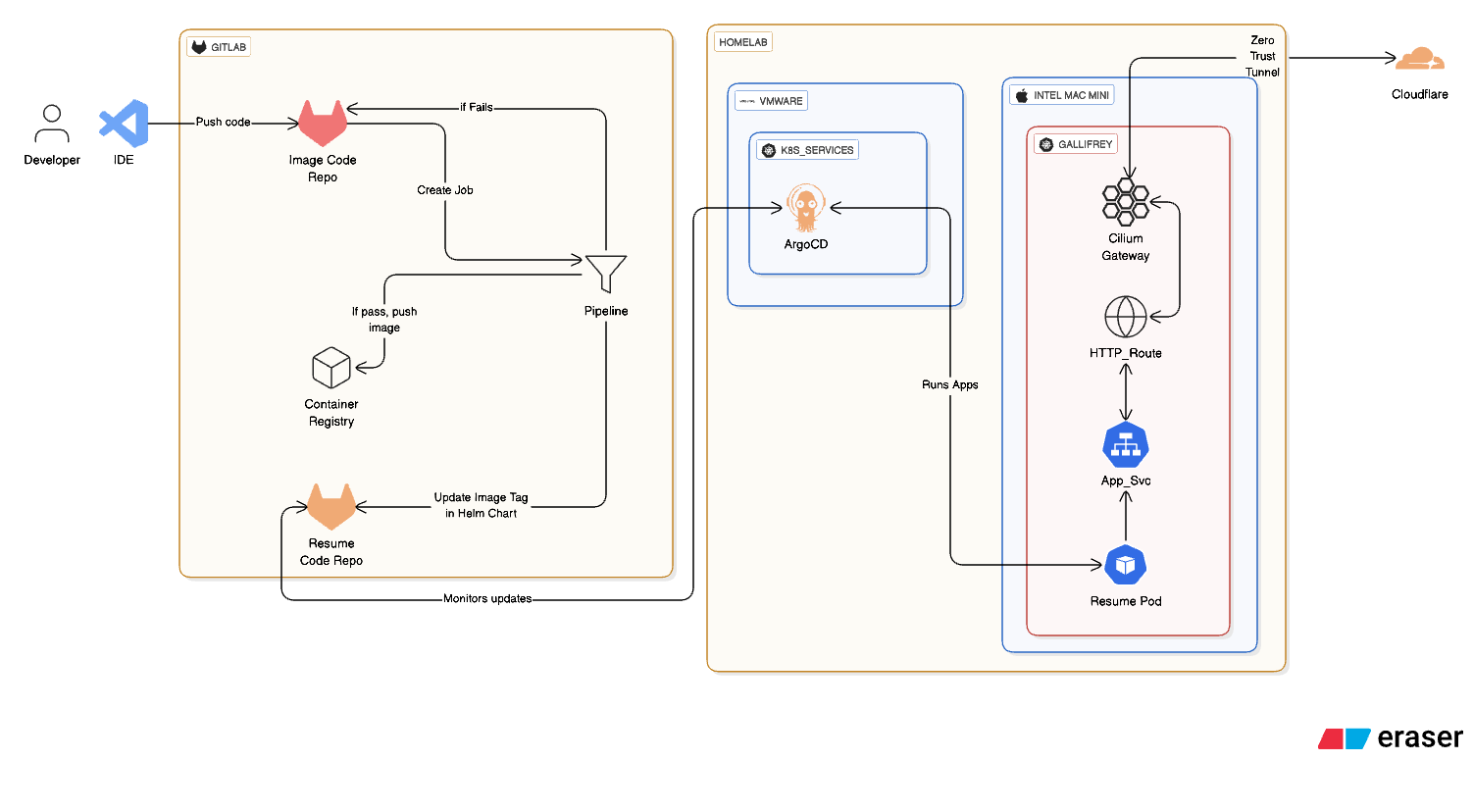
This diagram represents the complete deployment path and mirrors the same patterns I use for every production workload in my lab.
Why Deploy a Resume App in Kubernetes?
Because resumes should not just say what you know. They should demonstrate it.
I wanted my resume to live inside the same environment I use to experiment with:
- GitOps workflows
- Immutable infrastructure
- Zero-trust networking
- Real ingress and DNS patterns
- Operational recovery and redeployments
If it breaks, I fix it the same way I would any production service.
The Application
The resume itself is intentionally simple.
The complexity is not in the app. It is in how it is deployed.
The repository includes:
- A containerized resume application
- Kubernetes manifests for deployment
- Service and ingress configuration
- Declarative definitions designed for GitOps workflows
Nothing is deployed manually. Git is the source of truth.
The Target Environment: Gallifrey
Gallifrey is my bare-metal Kubernetes cluster running on Talos Linux.
- Immutable, API-driven OS
- No SSH access
- No configuration drift
- Everything managed declaratively
This cluster represents my production homelab environment. It is the place where changes are expected to be intentional and repeatable.
GitOps Flow with ArgoCD
The deployment flow looks like this:
- Code change committed to Git
- ArgoCD detects drift
- Manifests are reconciled automatically
- Application deploys or updates
- Health and sync status validate the rollout
No kubectl apply.
No manual fixes.
If something breaks, the fix goes into Git.
That constraint is intentional. It forces clarity and discipline.
Networking and Exposure
Ingress is handled using Cilium and the Kubernetes Gateway API, keeping routing consistent across internal and external services.
External access is provided via Cloudflare Tunnels, which means:
- No inbound ports opened on my home network
- No public load balancers
- Zero-trust access by design
The application is reachable externally, but the cluster itself remains sealed off.
Why This Matters
This deployment reinforced something I strongly believe:
Build what is needed, using what you have.
Rather than over-building, the goal was to recreate a production-style flow at a smaller scale. The same GitOps patterns, the same networking model, and the same operational expectations, applied to a simple application.
Running a small application through a full GitOps pipeline exposes issues you will never see in a tutorial:
- Misconfigured health checks
- Broken ingress assumptions
- Namespace and RBAC mistakes
- Resource limits you did not think about
- How recovery actually works when something goes sideways
Those lessons transfer directly to real environments.
Lessons Learned
A few things this deployment reminded me of:
- GitOps removes memory from the equation. Git always knows.
- Clean manifests matter more than clever ones.
- Networking problems often look like application bugs.
- Immutable systems reward preparation, not panic.
- Treating everything like production changes how you think.
Closing Thoughts
This resume app is not special because of what it shows on the screen.
It is special because of where and how it runs.
It lives in the same ecosystem as everything else in my lab. Versioned, observable, recoverable, and boring in the best possible way.
That is the goal.
If you want to explore the code and manifests used for this deployment, you can find the repository here:
https://gitlab.com/cybersecuritybro/resume-cybersecuritybro/
Do Not Quit On Yourself. Build it, break it, and build it better.